#verification
#verification
[ follow ]
#social-media #bluesky #automation #ai #reddit #digital-services-act #decentralization #generative-ai
fromFast Company
3 months agoWhat is AI.com? Mysterious website asks for people's credit card information after Super Bowl ad
The new AI platform, founded by Crypto.com CEO and co-founder Kris Marszalek, reportedly spent a whopping $85 million on the Super Bowl spot, only to garner so much traffic that he had to post on X: "Insane traffic levels. We prepared for scale, but not for THIS," followed by three fire emojis.
Artificial intelligence
fromExchangewire
3 months agoBlasto Ad Tech Ecosystem Releases 2025 Results Focused on Supply Control & DSP Launch
Blasto, a global programmatic advertising ecosystem, has reported its 2025 operational results, outlining platform developments across demand-side tooling, verification infrastructure, and service innovations, as well as the launch of a new DSP offering designed for small and mid-sized agencies. According to the company, 2025 marked a deliberate shift from surface-area expansion to workflow clarity, controllability, and measurable supply quality, reflecting buyer demand for tighter SPO outcomes, reduced auction noise, and consistent policy enforcement across mobile app and CTV environments.
Marketing tech
fromBusiness Insider
3 months agoHow Minneapolis' newspaper is reporting on ICE chaos - after everyone's already seen the video
The Minnesota Star Tribune is the state's biggest newspaper, and has been doing an excellent job of covering every angle of "Operation Metro Surge" - the federal government's mass deportation effort that started in December. But it is also competing in a real-time news environment where everyone is a reporter, and cellphone videos and social media posts are widely distributed.
Media industry
fromPoynter
5 months agoTrump says the US secured at least $18 trillion worth of investments this year. That's wrong - Poynter
On his second day in office, Jan. 21, Trump said the U.S. had "already secured nearly $3 trillion of new investments." By May 8, that figure rose to "close to $10 trillion." It eventually peaked Oct. 29 during a meeting with South Korean Prime Minister Kim Min-seok: "I think by the end of my first term, we should have $21 or $22 trillion dollars invested in the United States from other people and countries," Trump said.
US politics
fromBusiness Insider
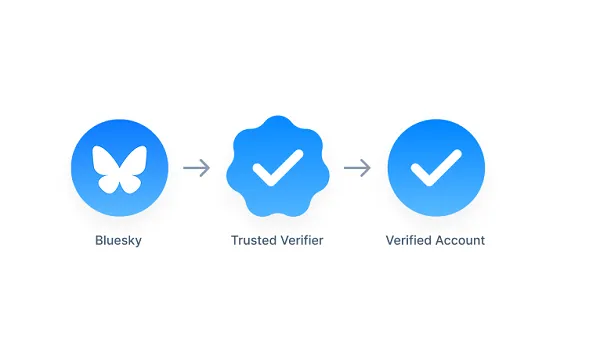
5 months agoElon Musk spent the weekend going after the EU after it fined X over 'deceptive' blue checkmarks
The billionaire unleashed a barrage of posts on X, boosting claims that cast Brussels as censorious, corrupt, and anti-democratic - just days after the bloc fined his platform €120 million ($140 million) over the "deceptive design" of its blue checkmarks. In one post, Musk asked followers: "How long before the EU is gone?" AbolishTheEU. In another instance, he backed a call for binding referendums on whether countries should remain in the bloc, describing it as a "good idea."
Careers
fromThe Drum
9 months agoTurning AI chaos into opportunity: Storyful's John Hall on the future of news
The news landscape of 2025 is a battlefield of fact versus fiction. As generative AI floods social feeds with increasingly plausible but fake content, the need for credible, verified information has never been more urgent.
Digital life
US politics
fromenglish.elpais.com
10 months agoAI swallows misinformation and spits it back at us: It's optimized to give useful information, but not for it to be correct'
AI chatbots struggle with real-time verification of information, potentially contributing to the spread of misinformation during events like the Los Angeles protests.
[ Load more ]