Information security
fromTechRepublic
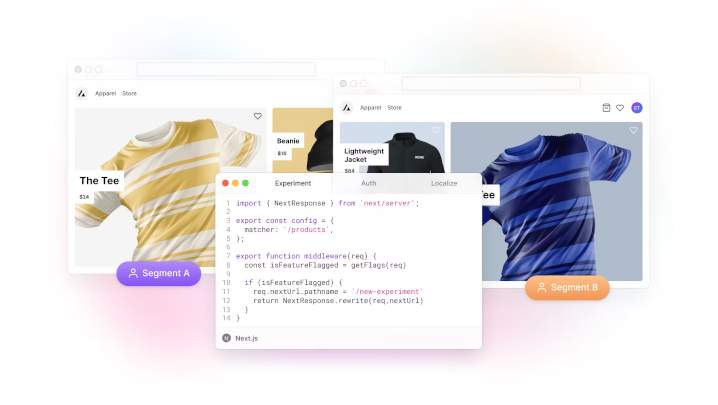
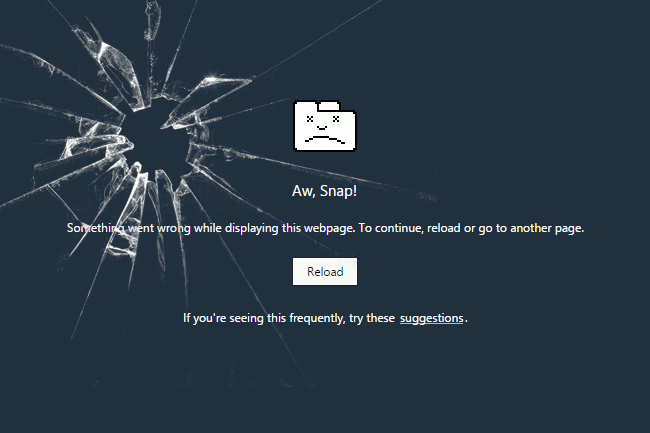
8 hours agoVercel Confirms Major Security Incident as Hacker Claims $2M Ransom Demand
Vercel confirmed a security incident involving unauthorized access to internal systems, with a threat actor claiming to sell stolen company data.