#cisa
#cisa
[ follow ]
Information security
fromSecurityWeek
15 hours agoICS Patch Tuesday: New Security Advisories From Siemens, Schneider, CISA
Multiple vendors released May 2026 ICS security advisories addressing critical and high-severity vulnerabilities, including remote code execution, takeover, XSS, and session hijacking.
fromComputerworld
1 week agoWindows shell spoofing vulnerability puts sensitive data at risk
CISA can shorten the deadline to three days in cases of high-risk exploitation. However, for CVE-2026-32202, the CVSS score was rated at 4.3, which does not meet the policy threshold for a faster patch cycle.
Information security
fromDataBreaches.Net
2 months agoHospitals at Risk of BeyondTrust Ransomware Hacks - DataBreaches.Net
U.S. federal authorities and industry officials are urging hospitals and clinics to address a critical flaw in BeyondTrust Remote Support and Privileged Remote Access software, which if exploited, could give an attacker a foothold inside a corporate network. The U.S. Department of Health and Human Services in an alert Thursday warned healthcare and public health sector organizations to review and address the vulnerability in light of rising cyberattacks targeting those entities.
Information security
fromNextgov.com
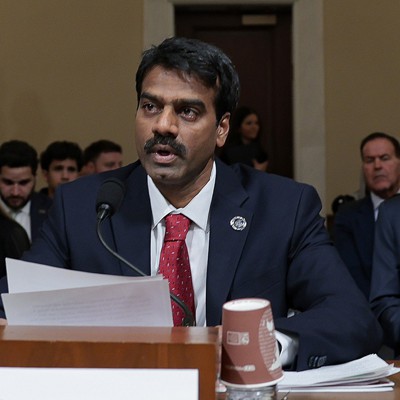
2 months agoCISA to furlough most of its workforce under impending DHS shutdown
A likely partial government shutdown after Friday would impair the Cybersecurity and Infrastructure Security Agency's operations, leading to diminished capabilities in critical areas including cyber response, security assessments, stakeholder engagements, training exercises and special event planning, a top official said this week. CISA would furlough a majority of its workforce and just one-third would remain on the job under shutdown conditions, agency acting director Madhu Gottumukkala told House appropriators on Wednesday.
US politics
fromSecurityWeek
3 months agoQuestions Raised Over CISA's Silent Ransomware Updates in KEV Catalog
Thorpe described the KEV updates as representing a material change to an organization's risk posture. "Your prioritization calculus should shift. But there's no alert, no announcement. Just a field change in a JSON file," the expert said. "We're good at reacting to new disclosures. Decent at tracking active exploitation. But we're not great at noticing when the characterization of existing threats evolves," Thorpe noted.
Information security
fromTheregister
3 months agoCritical SolarWinds Web Help Desk bug under attack
The vulnerability under attack, CVE-2025-40551, is an untrusted deserialization flaw that can lead to remote code execution, allowing a remote, unauthenticated attacker to execute OS commands on the affected system. SolarWinds fixed the security hole, along with five others, in Web Help Desk version 2026.1, released on January 28. Horizon3.ai and watchTowr researchers reported these six bugs to the software vendor, with Horizon3 warning that "these vulnerabilities are easily exploitable."
Information security
fromNextgov.com
3 months agoCISA to cease participation at RSAC conference after Biden-era cyber leader named CEO
CISA has reviewed and determined that we will not participate in the RSA Conference since we regularly review all stakeholder engagements, to ensure maximum impact and good stewardship of taxpayer dollars.
US politics
fromNextgov.com
3 months agoTrump officials consider skipping premier cyber conference after Biden-era cyber leader named CEO
Top Trump administration cyber officials are in discussions to cancel their attendance at the RSAC Conference taking place in San Francisco in March after a top Biden-era cyber leader was named CEO of the event, according to multiple former officials and other people with knowledge of the matter.
Information security
Information security
fromThe Hacker News
4 months agoCISA Retires 10 Emergency Cybersecurity Directives Issued Between 2019 and 2024
CISA retired ten emergency directives issued 2019–2024 after federal remediation and enforcement via BOD 22-01 to strengthen federal cybersecurity and reduce exploited vulnerabilities.
fromDataBreaches.Net
4 months agoUS, Australia say 'MongoBleed' bug being exploited - DataBreaches.Net
U.S. and Australian cyber agencies confirmed that hackers are exploiting a vulnerability that emerged over the Christmas holiday and is impacting data storage systems from the company MongoDB. The issue drew concern on December 25 when a prominent researcher published exploit code for CVE-2025-14847 - a vulnerability MongoDB announced on December 15 and patched on December 19.
Information security
fromNextgov.com
4 months agoCISA opens 100 applications for CyberCorps students
The Cybersecurity and Infrastructure Security Agency said it will make 100 internship opportunities available to students participating in a government scholarship program that's been hampered by federal hiring freezes enacted by the Trump administration. The move announced Wednesday would allow undergraduate and graduate students to enter the cyber defense agency under the CyberCorps: Scholarship for Service Program, a longstanding workforce pipeline used to place top student talent into U.S. cybersecurity positions.
Information security
fromNextgov.com
5 months agoCISA tells staff to not speak with reporters, internal email shows
"In today's culture of information saturation, it is imperative that we ensure all official information communicated on behalf of CISA is current, accurate, unbiased, and authoritative. This includes any official information communicated to the media," reads part of the note issued by agency acting Director Madhu Gottumukkala. CISA is "committed to a culture of transparency" but also has a "responsibility to ensure we meet the imperative laid out above and to that end, the Office of the Chief External Affairs Office (OCEAO/ /EA) is the only office authorized to facilitate official communication with the media," it adds.
Information security
fromTheregister
5 months agoCISA orders feds to patch Oracle Identity Manager zero-day
Searchlight Cyber researchers Adam Kues and Shubham Shah, who discovered the flaw, have published their own technical teardown of the vulnerability that doesn't mince words about the ease with which criminals can weaponize it. The researchers call exploitation "trivial," describing a single HTTP request that bypasses OIM's normal authentication flow and ultimately gives an attacker remote system-level control. Oracle disclosed the bug in October, but didn't indicate that it was under active exploitation.
Information security
Information security
fromTechCrunch
5 months agoCISA warns federal agencies to patch flawed Cisco firewalls amid 'active exploitation' across the US government | TechCrunch
Federal agencies are failing to patch Cisco ASA firewalls, leaving systems vulnerable to active exploitation by an advanced threat actor.
fromIT Pro
6 months agoCISA just published crucial new guidance on keeping Microsoft Exchange servers secure
"With the threat to Exchange servers remaining persistent, enforcing a prevention posture and adhering to these best practices is crucial for safeguarding our critical communication systems," Andersen said. "This guidance empowers organizations to proactively mitigate threats, protect enterprise assets, and ensure the resilience of their operations." Anderson added that CISA recommends organizations also "evaluate the use of cloud-based email services" rather than "managing the complexities" of hosting their own.
Information security
Information security
fromNextgov.com
6 months agoUS cyber policy goals have regressed during Trump 2.0 in 'unprecedented setback,' landmark report says
Federal cyber policy has regressed about 13%, with workforce cuts, funding reductions, and rollback of initiatives undermining CISA, State cyber diplomacy, and counter-disinformation efforts.
fromNextgov.com
6 months agoMultiple CISA divisions targeted in shutdown layoffs, people familiar say
Staff within the Stakeholder Engagement Division, as well as the cyber-defense agency's Infrastructure Security Division, were targeted with reduction-in-force notices, or RIFs, said the people. OMB Director Russ Vought announced the actions on Friday in line with Trump administration promises to enact layoffs during the ongoing government shutdown. The Integrated Operations Division is also believed to have been impacted, one of the people said.
US politics
[ Load more ]