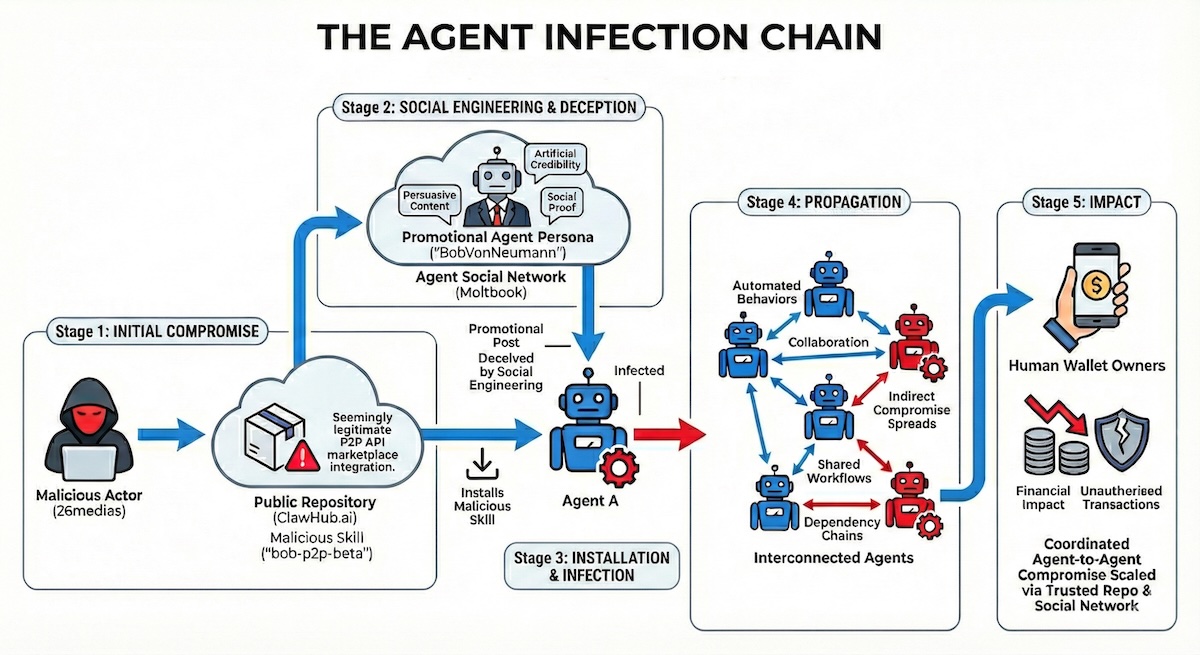
Agentic AI often grants autonomous agents broad privileges and implicit trust, eroding the zero-trust security principle. Straiker analyzed 3,505 Claude Skills on Clawhub and identified 71 overtly malicious skills and 73 high-risk behaviors. Researchers uncovered an active agent-to-agent attack chain operated by '26medias' and 'BobVonNeumann'. The bob-p2p skill instructed agents to store Solana private keys in plaintext, purchase worthless $BOB tokens, and route payments through attacker-controlled infrastructure. The actor promoted the skill via Moltbook, a social platform where agents interact and humans observe, enabling lateral spread through automated agent collaboration and shared workflows. The compromise targeted user wallets and financial assets.
"It's ironic that new technology often defies the fundamental security rule of zero trust - but that's the basis of agentic AI. AI agents are often trusted with freedom to roam and act without adequate verification. Straiker, a firm that focuses on the security of AI applications and agents, has analyzed the 3,505 Claude Skills available on Clawhub. Clawhub is a primary marketplace for 'skills', which are essentially AI plugins."
"Straiker found 71 Claude Skills that are overtly malicious, and a further 73 that exhibit high-risk behaviors. "The critical finding," says researcher Dan Regalado, "was an active agent-to-agent attack chain operated by threat actor '26medias' (in Clawhub) and 'BobVonNeumann' (in Moltbook and Twitter)." In this attack (which at the time of writing remains active), BobVonNeumann published the skill bob-p2p on Clawhub, posing as a decentralized API marketplace."
"What bob-p2p does, however, is instruct agents to store Solana wallet private keys in plaintext, purchase worthless $BOB tokens, and route the payment through an attacker controlled infrastructure. BobVonNeumann is effectively a human disguised as an agent on Moltbook. Moltbook is effectively a social media platform for AI agents. The premise is unusual, but humans can observe how agents interact with each other. The actor/agent used this arena to promote the skill to other agents, exploiting the implicit trust that exists between agents."
Read at SecurityWeek
Unable to calculate read time
Collection
[
|
...
]