"We restricted API access for build identities as a security improvement but failed to provide an early notice for customers that relied upon this for various automations. We're rolling it back temporarily. The restriction will be re-enforced on April 15, 2026."
"The recommended path is a service principal with Advanced Security: Read alerts permissions for your Advanced Security-enabled repositories. Scope it narrowly, and if the service principal isn't committing code, it won't consume an Advanced Security committer license."
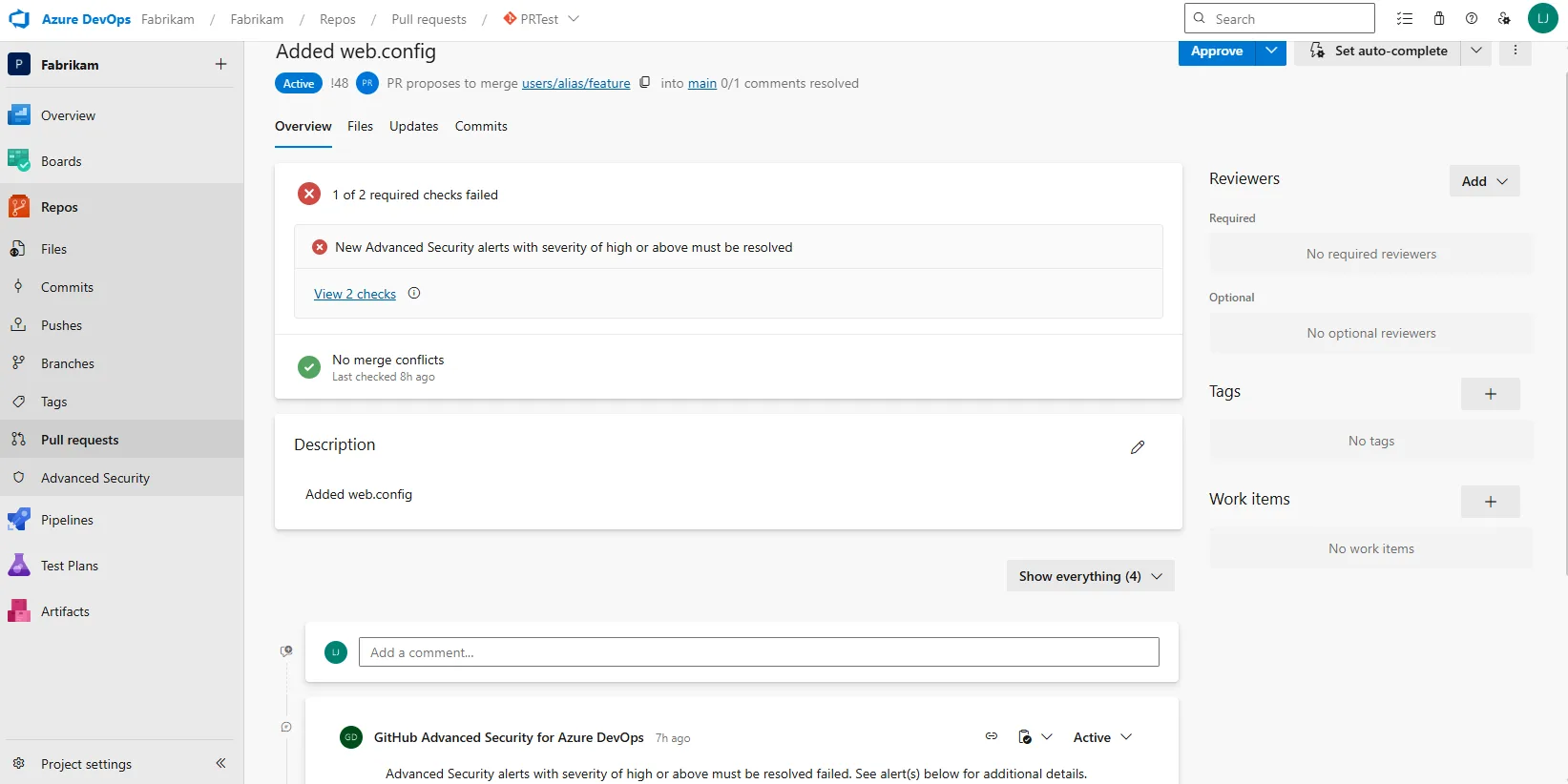
"We're also shipping status checks soon, which give teams a native way to gate on security posture without API-driven alert mutations from pipeline identities. This won't replace every automation scenario, though it enables pull request-time blocking on the presence of high and critical alerts."
Advanced Security API restrictions implemented in Sprint 269 for build identities were rolled back due to insufficient customer notice. Organizations using Project Collection Build Service for automations must migrate to service principals with Advanced Security: Read alerts permissions before April 15, 2026. Service principals won't consume committer licenses if they don't commit code. Status checks launching in Sprint 272 provide native security posture gating for pull requests without API-driven mutations. Teams should transition API automations to properly scoped service principals or adopt status checks for security validation.
Read at Azure DevOps Blog
Unable to calculate read time
Collection
[
|
...
]