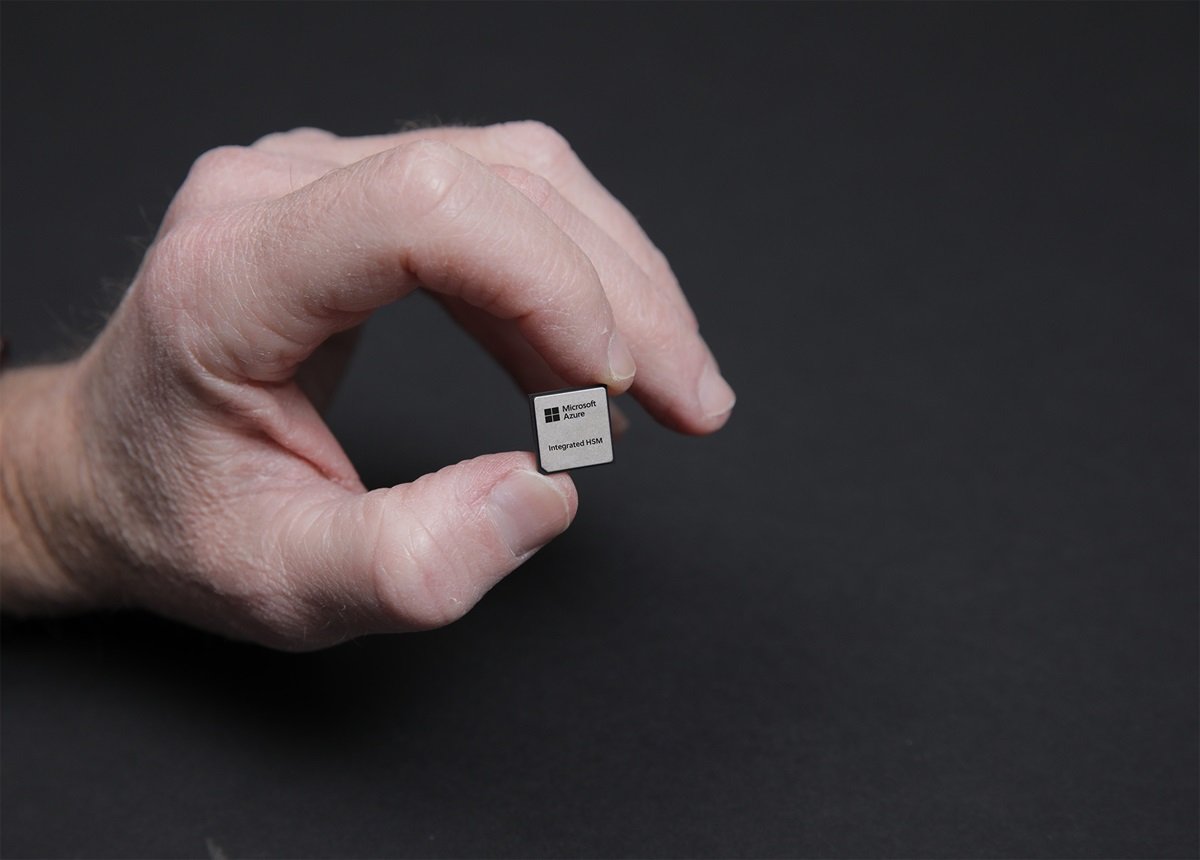
"A key aspect of Microsoft's hardware security is isolation. Encryption keys are stored in an integrated hardware security module (HSM), while VMs are isolated from one another using trusted execution environments (TEE) baked into modern CPUs and GPUs. The control, data, networking, and storage planes are all offloaded to smartNICs and an open source Root of Trust (RoT) module ensures everything is what it purports to be."
"HSMs aren't new by any stretch of the imagination, and serve as a vault for storing and executing cryptographic keys and operations. Traditionally, Kelly explained, HSMs have been dedicated appliances which might serve multiple systems and virtual machines. However, this approach presents several challenges. "They're specialized hardware that are deployed separately in separate clusters, and this can create some challenges with scaling them as the compute and AI infrastructure is deployed," he said. "Another challenge is they're remotely accessed. When a workload wants to access its keys that are stored in HSM, it has to do a TLS connection to the HSM, ask it to perform an operation with the key, and then return the data. That creates latency... so, it becomes impractical for some workloads," Kelly added."
Microsoft secures Azure compute through a layered silicon security design emphasizing isolation. Encryption keys are stored in integrated hardware security modules (HSMs) adjacent to compute, while virtual machines use trusted execution environments (TEEs) in CPUs and GPUs for process isolation. Control, data, networking, and storage planes are offloaded to smartNICs. An open-source Root of Trust (RoT) module, including Caliptra 2.0, attests firmware and component integrity and is standard in the 2025 Azure fleet. Traditional centralized HSM appliances introduce scaling and latency challenges because they require remote TLS access for key operations; disaggregation addresses those limits.
Read at Theregister
Unable to calculate read time
Collection
[
|
...
]