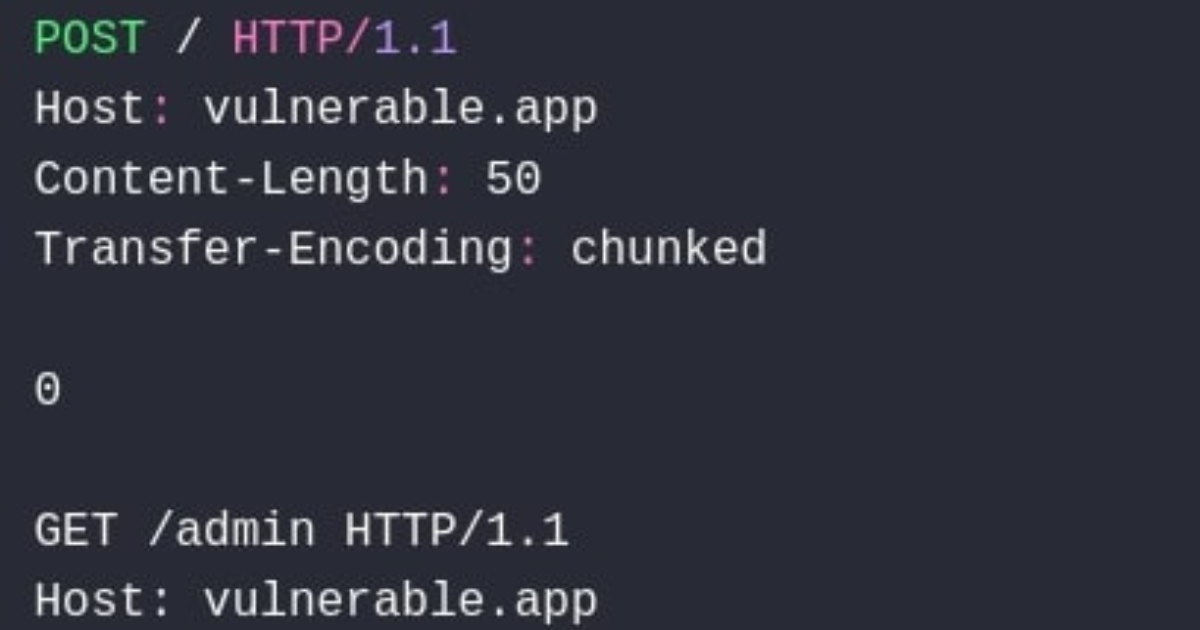
"The vulnerability has been identified in ASP.NET Core versions 10.0, 9.0, 8.0, and the Kestrel package for 2.x. An attacker who is already authorized can bypass a security feature by exploiting inconsistent parsing of HTTP requests and responses. Microsoft states there are no known mitigating factors for the HTTP request/response smuggling scenario and strongly recommends patching to the listed fixed versions to prevent the security bypass."
"The 9.9 score reflects the importance of promptly addressing this issue, which involves a security feature bypass that can influence how applications enforce authentication and authorization. (...) Depending on how your app processes requests, this could enable techniques like privilege escalation or request manipulation if left unpatched."
"The bug enables HTTP Request Smuggling, which on its own for ASP.NET Core would be nowhere near that high, but that's not how we rate things. Instead, we score based on how the bug might affect applications built on top of ASP.NET."
Microsoft patched a critical ASP.NET Core vulnerability CVE-2025-55315 with a CVSS score of 9.9. Affected packages include ASP.NET Core 10.0, 9.0, 8.0 and Kestrel 2.x. An attacker who is already authorized can bypass authentication or authorization controls by exploiting inconsistent parsing of HTTP requests and responses, enabling HTTP request smuggling. No known mitigations exist for the request/response smuggling scenario. Immediate patching to the fixed versions is strongly recommended. The high severity reflects how the bypass could enable privilege escalation or request manipulation depending on application request handling and impact on applications built on ASP.NET.
Read at InfoQ
Unable to calculate read time
Collection
[
|
...
]