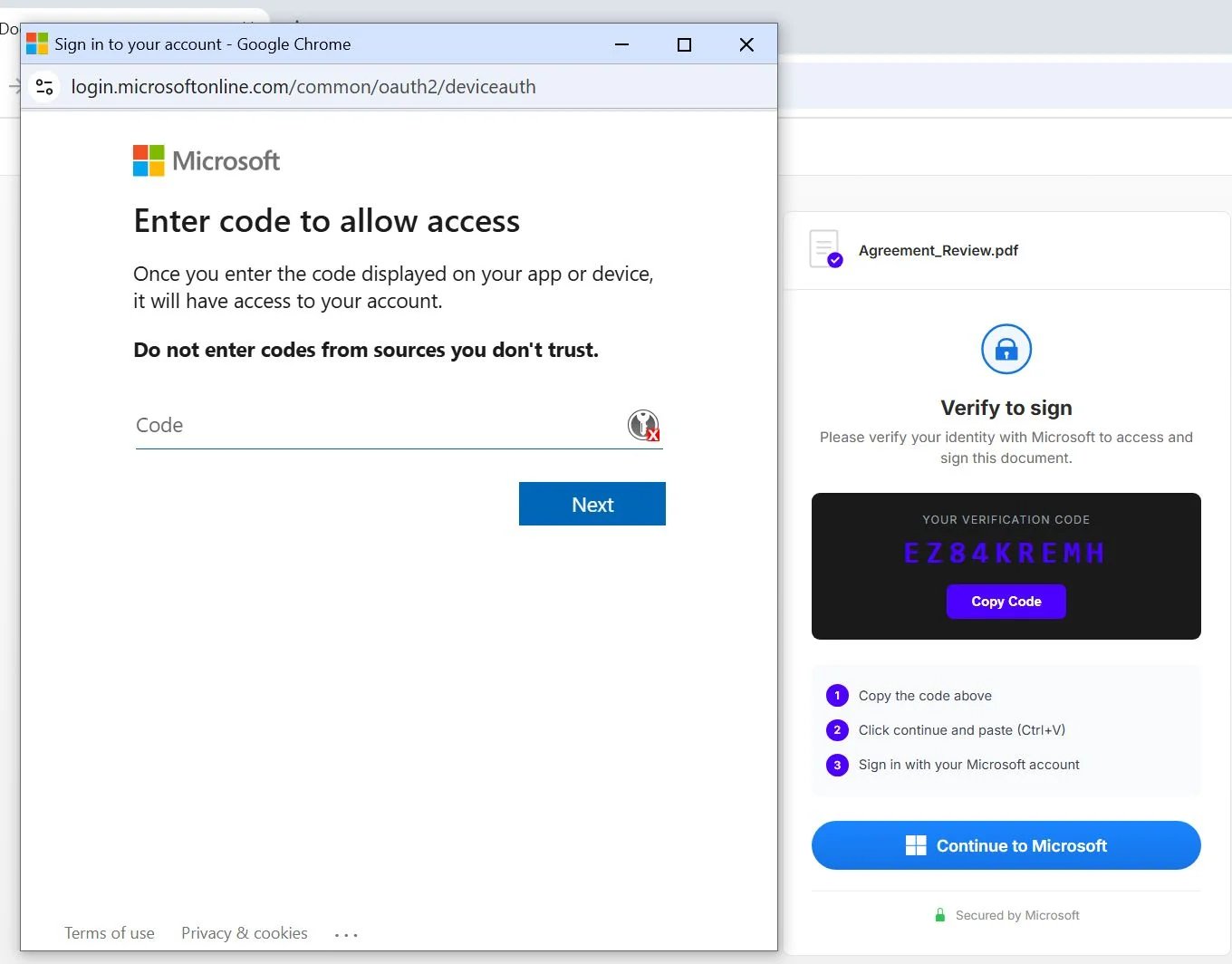
"This isn't your average 'click this link to reset your password' scam. Instead, it exploits a legitimate Microsoft feature called the OAuth device authorization flow, originally designed for devices that are hard to type on, like a smart TV or a printer."
"According to Huntress, 'Multi-factor authentication is not an effective mitigation for this attack because the victim inputs the code, then their username and password, and then MFA code if applicable. The resulting authentication generates a token that the attacker can retrieve, thus negating the protection of MFA.'"
"What makes this campaign particularly unusual is the infrastructure behind it. All the attacks Huntress observed are coming through Railway.com, a platform-as-a-service provider that markets itself to 'vibe coders' and beginners."
A phishing campaign targeting Microsoft 365 accounts has impacted over 340 organizations in the U.S., Canada, Australia, New Zealand, and Germany. The attack exploits the OAuth device authorization flow, allowing attackers to gain access to accounts even with multi-factor authentication enabled. Victims are tricked into entering a code on Microsoft's login page, granting attackers a token for up to 90 days. The campaign utilizes Railway.com, a platform that simplifies application deployment, making it easier for attackers to execute their schemes.
Read at TechRepublic
Unable to calculate read time
Collection
[
|
...
]