"It's highly sophisticated, took millions of dollars to develop, and it bears the hallmarks of other modules that have been publicly attributed to the US government. This is the first example we've seen of very likely US government tools - based on what the code is telling us - spinning out of control and being used by both our adversaries and cybercriminal groups."
"We see no evidence of actual code reuse in the published reports to support attributing Coruna to the same authors."
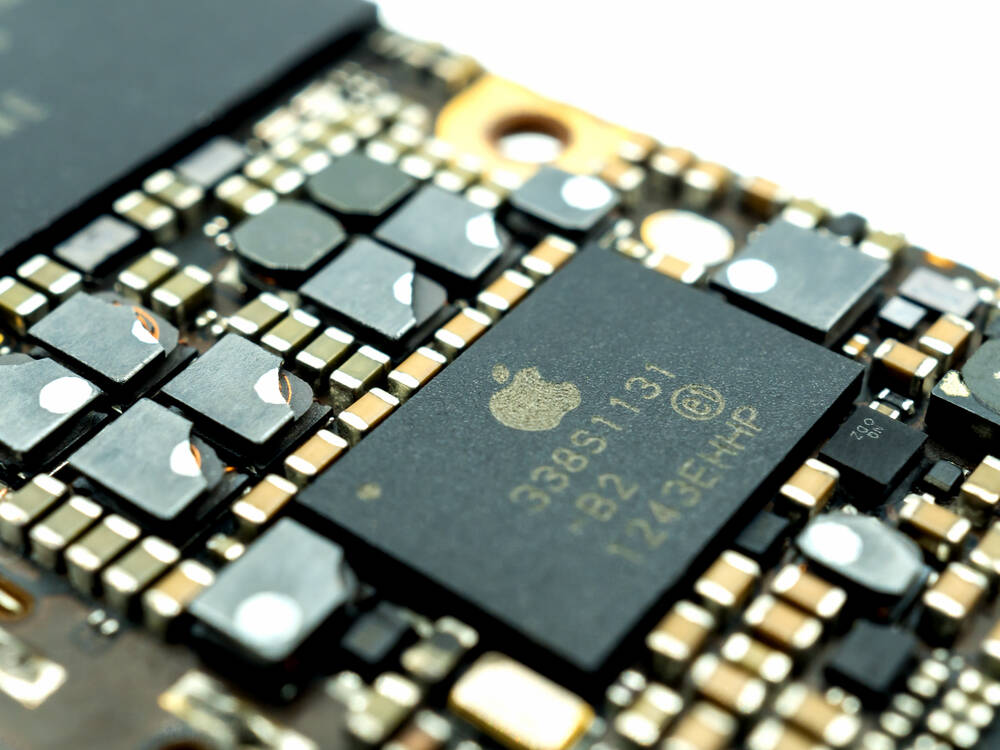
"Google said that around a year ago it identified a highly sophisticated and previously unknown iPhone exploit kit, perhaps used by commercial spyware vendors and/or state-sponsored hackers, that could bork a device if a user visited a website."
Google's Threat Intelligence Group discovered Coruna, a sophisticated iPhone exploit kit used in attacks across Ukraine and China over the past year. The kit contains 23 vulnerabilities and could compromise devices through malicious websites. Some cybersecurity experts, including iVerify's cofounder, suggested US government involvement based on the exploit's sophistication and similarities to previously attributed NSA tools. However, Kaspersky's principal security researcher Boris Larin rejected these attributions, stating no evidence supports linking Coruna to the same authors behind Operation Triangulation, the 2023 campaign allegedly targeting Russian diplomats.
#iphone-exploit-kit #cybersecurity-attribution #nsa-allegations #coruna-vulnerability #state-sponsored-hacking
Read at Theregister
Unable to calculate read time
Collection
[
|
...
]