"Email attackers are now targeting their victims with tailored tactics that exploit trusted relationships and routine workflows, making traditional detection methods less effective."
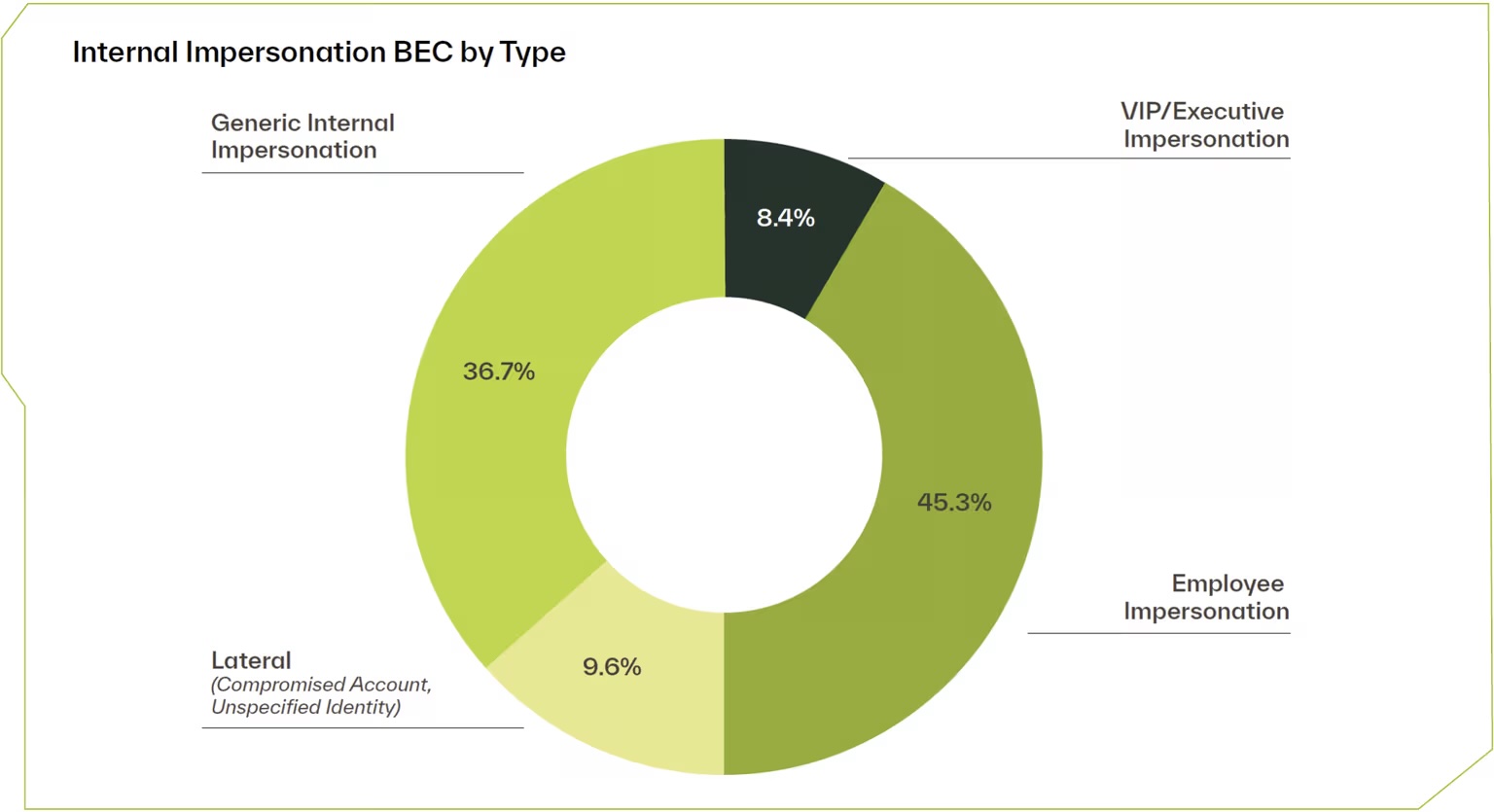
"Phishing remains predominant, accounting for 58% of all attacks, while business email compromise (BEC) comprises 11% and vendor email compromise (VEC) accounts for over 60% of BEC attacks."
"More than 20% of phishing attacks use redirect chains to obscure the final malicious page from both users and their security tools, complicating detection efforts."
"BEC and VEC are less frequent but involve more attacker craftsmanship, making them potentially more impactful than phishing attacks."
Email attacks have evolved, with attackers focusing on behavioral and organizational weaknesses rather than technical vulnerabilities. Phishing is the most common method, making up 58% of attacks, followed by business email compromise (BEC) at 11%. Phishing tactics vary by target, often using file-sharing lures and brand impersonation to blend into normal workflows. More than 20% of phishing attacks utilize redirect chains to hide malicious pages. BEC and vendor email compromise (VEC) are less frequent but can have a greater impact on organizations.
Read at SecurityWeek
Unable to calculate read time
Collection
[
|
...
]