"Visual Deception: The echo command prints a fake URL (dl.github.com/...) to the terminal. This does absolutely nothing functionally, but it tricks the user into thinking a legitimate GitHub download is initiating. URL Obfuscation: The actual malicious URL is hidden using Base64 encoding. Once decoded, it reveals https://peowqitisuuus.com/debug/loader.sh?build=75d397ce9c31a090223b8a940947c3ce-a domain completely unrelated to GitHub. Blind Execution: By piping (|) the curl output directly into zsh, the script executes instantly in memory, depriving the user of any chance to review the code before it runs."
"Instead of a standard download button, it prompts users to run a "Terminal installation" command. In reality, this command is a multi-layered obfuscated dropper. The final payload is a fully-featured, aggressive macOS information stealer that identifies itself internally as SHub Stealer (Build i1b)."
"Stage One: The Loader ScriptBy safely extracting the payload (swapping | zsh for > file.s"
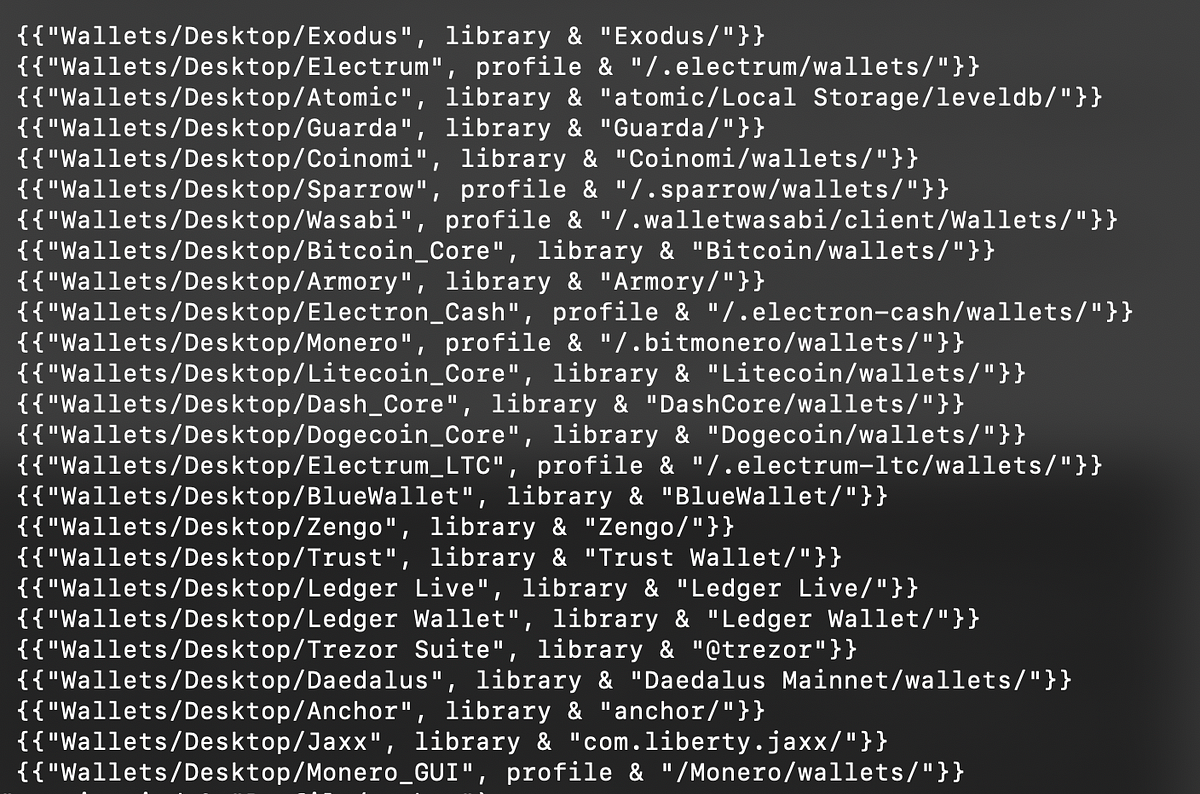
A phishing page imitates the official GitHub Desktop macOS download page and includes a fake “Verified Publisher” badge. Instead of a normal download, it instructs users to run a “Terminal installation” command. The command uses multiple deception techniques: it prints a harmless-looking GitHub URL, hides the real malicious URL using Base64 encoding, and executes the downloaded content immediately by piping it into zsh. The decoded URL retrieves a loader script that further obfuscates behavior through multiple layers. The final stage delivers a fully featured macOS information stealer that identifies itself internally as SHub Stealer (Build i1b).
Read at Medium
Unable to calculate read time
Collection
[
|
...
]