"The vault is solid. The delivery truck is not. Once the user has authenticated, the system passes Recall data to another system process called AIXHost.exe, which doesn't benefit from the same security protections."
"The TotalRecall Reloaded tool uses an executable file to inject a DLL file into AIXHost.exe, something that can be done without administrator privileges. It can intercept screenshots, OCR'd text, and other metadata that Recall sends to AIXHost.exe."
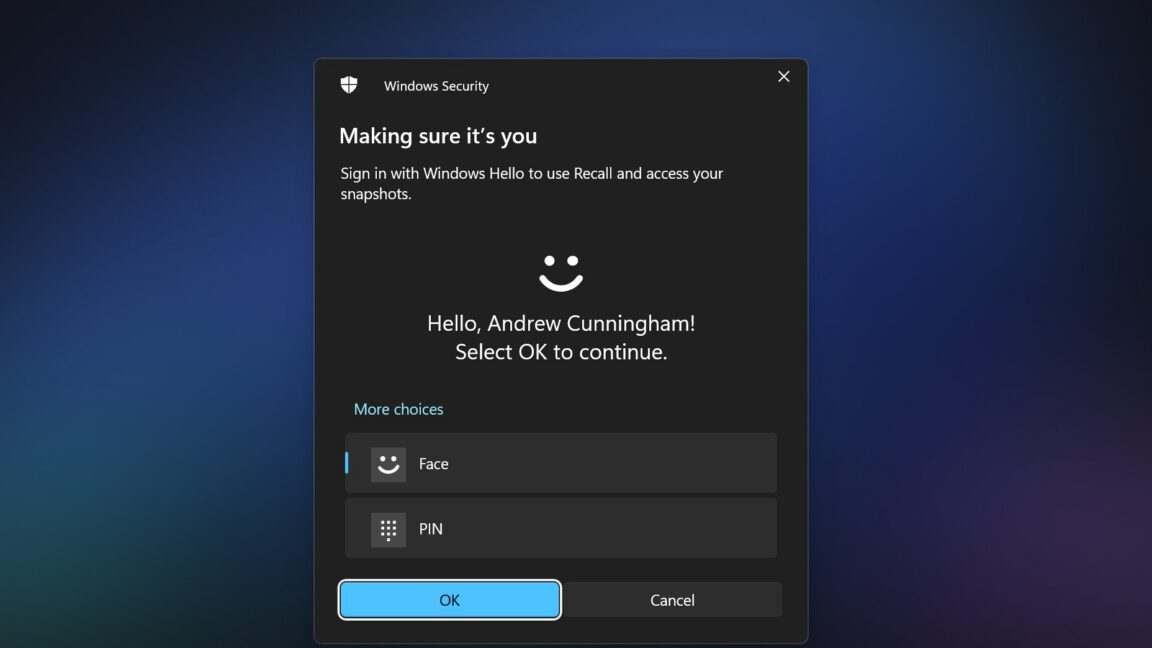
"A handful of tasks, including grabbing the most recent Recall screenshot and deleting the user's entire Recall database, can be done with no Windows Hello authentication. Once authenticated, the tool can access both new and previously recorded information."
"Microsoft has said that Hagenah's discovery isn't actually a bug and that the company doesn't plan to fix it. They classified it as 'not a vulnerability' after reviewing the findings."
The Recall database is secure, but the AIXHost.exe process does not have the same security measures. The TotalRecall Reloaded tool can inject a DLL into AIXHost.exe without admin rights, allowing it to intercept data after user authentication. Tasks like capturing screenshots and deleting the Recall database can occur without Windows Hello authentication. Microsoft has classified this issue as not a vulnerability and does not plan to address it, despite concerns raised by Hagenah regarding the security risks involved.
Read at Ars Technica
Unable to calculate read time
Collection
[
|
...
]