"The gateway binds to localhost by default, based on the assumption that local access is inherently trusted. That assumption is where things break down. Because WebSocket connections to localhost were not blocked by the browser's cross-origin policies, JavaScript code on a malicious website could open such a connection using the agent's port."
"The gateway's rate limiter completely exempts loopback connections-failed attempts are not counted, not throttled, and not logged. In our lab testing, we achieved a sustained rate of hundreds of password guesses per second from browser JavaScript alone. At that speed, a list of common passwords is exhausted in under a second, and a large dictionary would take only minutes."
"It could then brute-force the password, because localhost connections were not covered by the gateway's rate limiter, and then register as a trusted device, as device pairings from localhost were automatically approved with no user prompt."
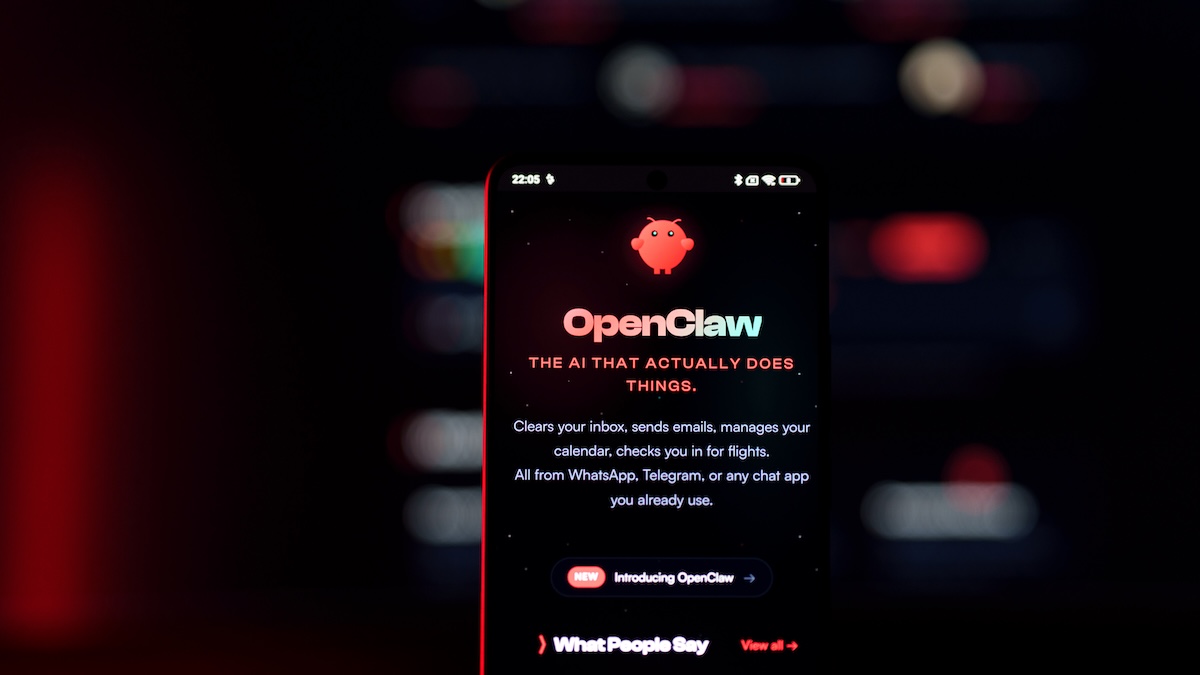
OpenClaw, a self-hosted AI agent, contains a critical vulnerability enabling attackers to hijack agents without requiring malicious extensions or user interaction. The vulnerability stems from the gateway's default binding to localhost with the assumption that local access is inherently trusted. WebSocket connections to localhost bypass browser cross-origin policies, allowing JavaScript from malicious websites to connect using the agent's port. The gateway's rate limiter completely exempts loopback connections, enabling attackers to brute-force passwords at hundreds of guesses per second. Once the password is compromised, attackers can register as trusted devices since device pairings from localhost are automatically approved without user prompts, granting full authenticated access to the agent.
#ai-security-vulnerability #openclaw #localhost-exploitation #password-brute-force #websocket-security
Read at SecurityWeek
Unable to calculate read time
Collection
[
|
...
]